Configure SSL certificates
Secure Sockets Layer (SSL) certificates enable secure communication between the BigFix WebUI server and all users that access it. Use this procedure to configure SSL certificates for BigFix WebUI.
Using self-signed SSL certificates
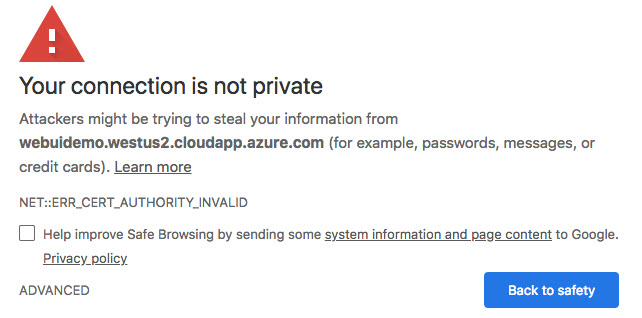
Consider purchasing officially signed SSL certificates by a certificate authority (CA) such as Verisign, Entrust, or ZeroSSL. The advantage of using an external CA is that root certificates of known public CAs are imported by default into modern web browsers.
Using SSL certificates from a trusted Certificate Authority
Configure certificates from a trusted certificate authority (CA) to use in your BigFix WebUI deployment. When generating a private key and a certificate signing request (CSR) for a CA signed certificate, ensure that the private key and the certificate files have the following format and structure:
- Private key format
- PEM-encoded and without a password protection. The pvk format is not supported. Ensure that the
private key (private.key) is enclosed between the following statements:
-----BEGIN PRIVATE KEY----- <<base64 string from private.key>> -----END PRIVATE KEY-----
- X509 certificate format
- PEM-encoded. If you have also received the intermediate and root certificates as separate files,
you should combine all of them into a single one. For example, if you have
the primary certificate file (certificate.crt) and the intermediate
certificate file (ca_intermediate.crt), ensure that you combine them
in the following order, primary certificate first followed by the
intermediate certificate:
If you received the root certificate (ca_root.crt) in addition to the intermediate certificate, combine them as follows:-----BEGIN CERTIFICATE----- <<primary certificate: base64 string from certificate.crt>> -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- <<intermediate certificate: base64 string from ca_intermediate.crt>> -----END CERTIFICATE----------BEGIN CERTIFICATE----- <<primary certificate: base64 string from certificate.crt>> -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- <<intermediate certificate: base64 string from ca_intermediate.crt>> -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- <<root certificate: base64 stringfrom ca_root.crt>> -----END CERTIFICATE-----
Deploying SSL certificates
To deploy the SSL certificates to the BigFix WebUI server:
- Rename SSL private key to
ssl.pvk. - Rename the SSL certificate to
ssl.crt. - Copy both files to the following location on your WebUI server:
Table 1. WebUI server directory for storing the certificate and private key Operating System WebUI Server WebUI Server Directory Windows BigFix Root Server C:\Program Files (x86)\BigFix Enterprise\BES Server\WebUI Remote Server C:\Program Files (x86)\BigFix Enterprise\BES WebUI\WebUI Linux BigFix Root Server /var/opt/BES Server/WebUI Remote Server /var/opt/BESWebUI/WebUI - On the WebUI machine, ensure that the following client settings are added and that their values
are the paths specified in Step 3:
- _WebUIAppEnv_WEB_CERT_FILE
- _WebUIAppEnv_WEB_KEY_FILE
For example, if your WebUI directory is C:\Program Files (x86)\BigFix Enterprise\BES WebUI:- The value of WEB_CERT_FILE should be C:\Program Files (x86)\BigFix Enterprise\BES WebUI\ssl.crt and
- The value of WEB_KEY_FILE should be C:\Program Files (x86)\BigFix Enterprise\BES WebUI\ssl.pvk
- Restart the BES WebUI Service.