Configure and Run Malware Scans
CPM for Mac provides two types of malware scans: On-Demand, and Real-Time. In addition, you can schedule On-Demand scans to automatically recur. You can apply the same scan to all endpoints, or create different scan configurations and apply them to different sets of endpoints based on whatever criteria you choose. Users can be notified before a scheduled or on-demand scan runs, but do not explicitly receive notifications whenever a detection occurs on their computer.
Detections are logged and available for review in CPM Reports.
As with most Tasks in the IBM BigFix Console, you can associate any of these scans with selected computers, users, or other conditions. As a result, you can define multiple scan settings and then attach a particular scan configuration to a given set of computers. Scan settings are saved in the CPM Dashboard.
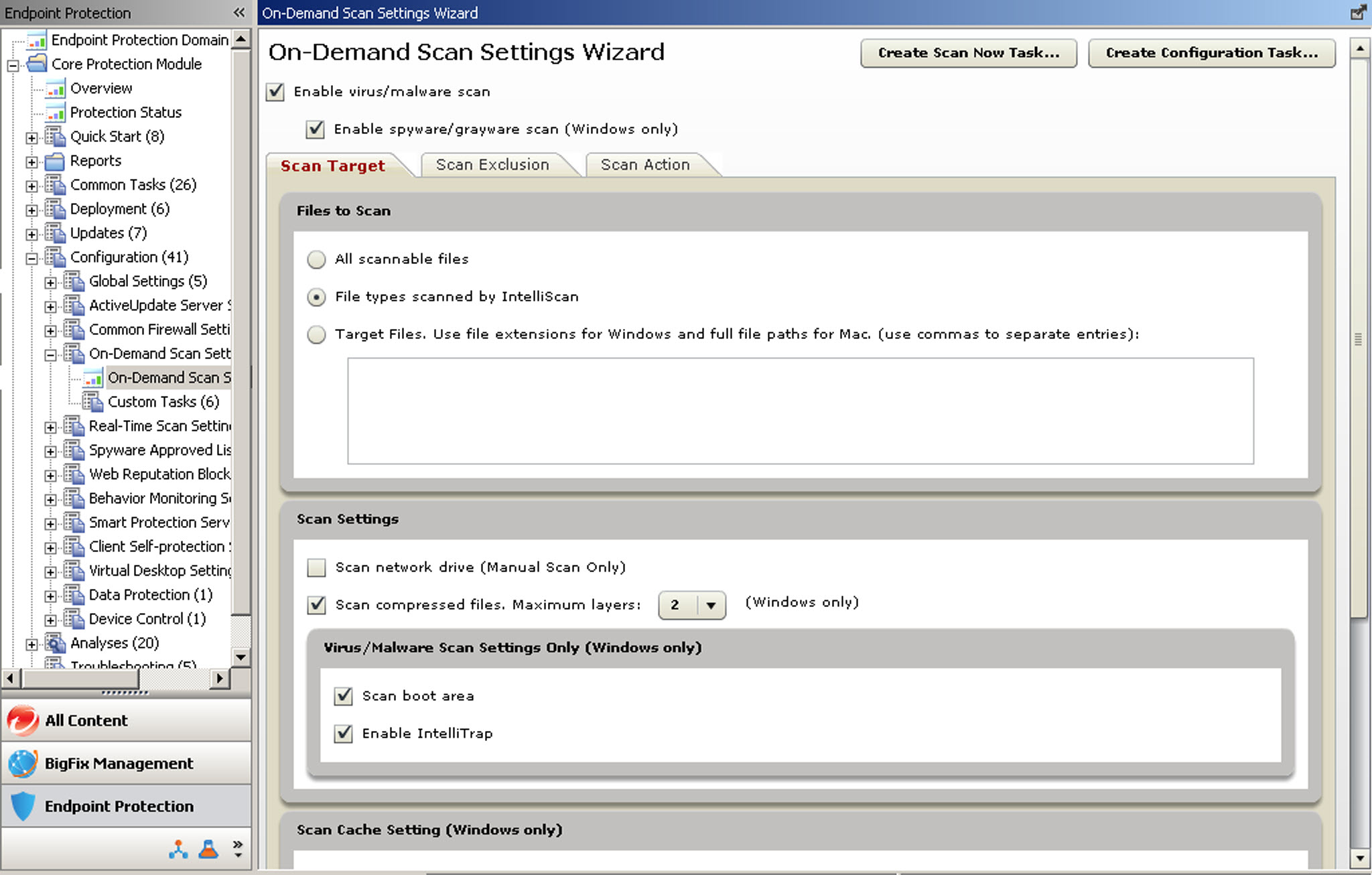
- On-Demand scans
- Use On-Demand scans to run a one-time scan of client hard drives or the boot sector. Launch the
default scan with the Scan Now Task. On-Demand scans can take from a few
minutes to a few hours to complete, depending on how many files are scanned and on client
hardware.Note: When an user initiates a Manual Scan from the CPM for Mac client console, the scan settings reflect the latest settings configured by the administrator for an On-Demand scan. For example, an administrator might schedule an On-Demand scan on every Thursday at 12:00 that scans all file types. Then the administrator might run an On-Demand scan with different scan settings, maybe scanning only for
.EXEfiles, at 14:00. If a user runs a Manual Scan at 15:00, and the administrator has not changed the settings, the user’s Manual Scan will scan only for.EXEfiles, not all file types. - Scheduled scans
- You can schedule an On-Demand scan to trigger at a particular time, day, or date. You can also have the scan automatically recur according to the schedule you set.
- Real-Time scans
- This scan checks files for malicious code and activity as they are opened, saved, copied, or otherwise being accessed. These scans are typically imperceptible to the user. Real-time scans are especially effective in protecting against Internet-borne threats and harmful files being copied to the client. Trend Micro recommends that you enable real-time scanning for all endpoints.
