Remediation
After risks are determined and vulnerabilities are prioritized, your security team can start the remediation process.
Basic remediation workflow: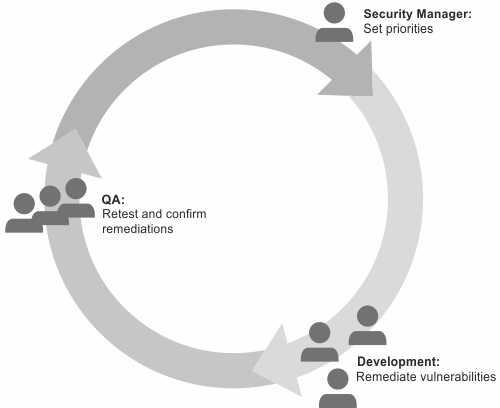
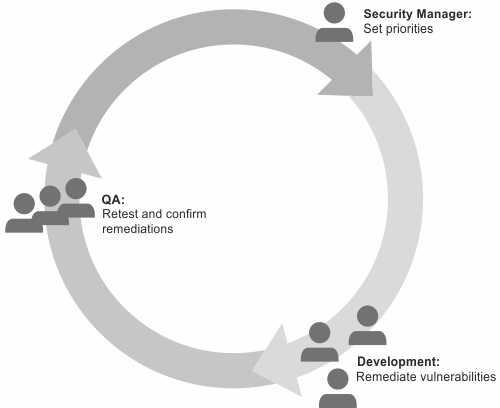
- The security manager sets priorities for remediation and assigns remediation tasks to the development team. If the possibility for exploitation is minimal, the security manager might decide to accept some degree of risk and not assign some vulnerabilities for remediation. Monitoring the situation for a set period might be the best course of action in some circumstances.
- Developers fix the highest priority vulnerabilities.
- QA engineers run the appropriate tests against the new version of the application, confirm that remediation was successful, and forward the data to the security manager.
There are other actions that security managers can take that go beyond fixing defects:
- Train developers on secure coding techniques.
- Provide code libraries that address the issues.
- Create test plans and scripts to detect defects early in the development lifecycle.
- Establish best practices for secure coding in application specifications.