Limiting scope of automated scan
![]() Available from 9.2.8.
To discover software that is installed on shared disks in your
infrastructure, create computer groups that contain only computers on which the same disk is
mounted. Then, scan one of the computers in that group to create a software template.
Finally, share the template between all computers on which the disk is mounted.
Available from 9.2.8.
To discover software that is installed on shared disks in your
infrastructure, create computer groups that contain only computers on which the same disk is
mounted. Then, scan one of the computers in that group to create a software template.
Finally, share the template between all computers on which the disk is mounted.
Before you begin
- This method of scanning is advised for environments with a heavy use of shared disks in which a
single shared disk is mounted on many computers. Important:
 Starting from application updated 9.2.12, this method can be automated. Using the automated
scanning is recommended as it is easier to set up and maintain. The difference is that automatic
mode scans all shared disks that exist in your environment. If you want to scan only selected shared
disks, use manual scanning. For more information, see: Discovering software on shared disks. If you already set up
manual scanning, you can switch to automatic scanning. For more information, see: Switching to automatic scanning of shared disks.
Starting from application updated 9.2.12, this method can be automated. Using the automated
scanning is recommended as it is easier to set up and maintain. The difference is that automatic
mode scans all shared disks that exist in your environment. If you want to scan only selected shared
disks, use manual scanning. For more information, see: Discovering software on shared disks. If you already set up
manual scanning, you can switch to automatic scanning. For more information, see: Switching to automatic scanning of shared disks.  You must be an Administrator to perform this task.
You must be an Administrator to perform this task.
About this task
- Scenario 1: Each computer has access to one shared disk
-
There are two shared disks, each mounted on six computers. To properly report the discovered software, create two computer groups in BigFix Inventory:
- Computer Group 1 that contains computers on which Shared Disk 1 is mounted
- Computer Group 2 that contains computers on which Shared Disk 2 is mounted
From each group, select one computer to be scanned. Scan results from the designated computer are propagated to the remaining computers in the computer group. Thus, software that is installed on Shared Disk 1 is reported on all computers in Computer Group 1 without the need to scan all computers in that group. The same happens for computers in Computer Group 2.
- Scenario 2: Some computers have access to two shared disks
-
There are two shared disks. Shared Disk 1 is mounted on nine computers. Shared Disk 2 is mounted on six computers. To properly report the discovered software, create two computer groups in BigFix Inventory:
- Computer Group 1 that contains computers on which Shared Disk 1 is mounted
- Computer Group 2 that contains computers on which Shared Disk 2 is mounted
Three of the computers belong to both computer groups because they have both disks mounted. Select one of these computers to be scanned. This way, only one computer is scanned to discover software that is installed on both shared disks. Scan results from the designated computer are propagated to the rest of computers in both groups. Computers on which only one disk is mounted show software from that disk only. Computers on which both disks are mounted show software from both disks.
- Scenario 3: Computers have access to one shared disk but run on different operating systems
-
There is one shared disk that is mounted on nine computers. Three of the computers run on Linux, three on AIX, and three on Solaris. To properly report the discovered software, create one computer group in BigFix Inventory. From this group, designate three computers to be scanned, one for every operating system.
It is necessary because the software catalog that is propagated to each computer monitored by BigFix Inventory contains software signatures specific to the operating system on which that computer runs. Thus, scan results from the shared disk must be matched against software catalog for every operating system. Scan results from each designated computer are propagated to the rest of computers that run on the same operating system.
Procedure
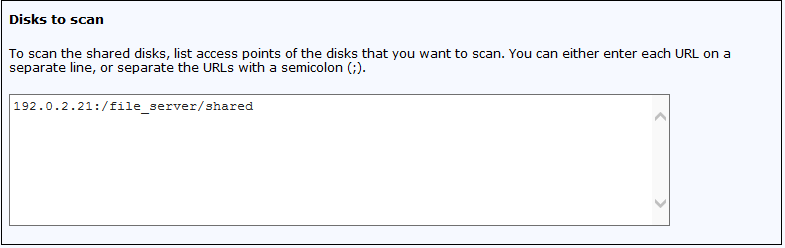
- Discover shared disks that exist in your infrastructure.
-
Create a list of unique access points of the discovered shared disks. The information is needed
to group computers on which the same shared disk is mounted.
-
Create a BigFix computer group that contains
computers on which a particular shared disk is mounted. The group is used to easily designate one
computer that can be scanned to create a software template.
-
From the computer group, choose one computer to be scanned. Information about software
discovered on the shared disk that is mounted on this computer is used as a software template.
-
If you have not previously scheduled upload of scan results from the scanned computer, schedule
it now. Ensure that the upload is scheduled only once per computer.
- In the navigation tree, click Fixlets and Tasks.
- In the upper right pane, select Upload Software Scan Results, and click Take Action.
- Select the computer that is scanned to create the software template, and click OK.
- To make the software templates available in BigFix Inventory, wait for the scheduled import or run it manually.
-
Create a computer group in BigFix Inventory. The group is
used to report software that is discovered on the shared disk on all computers that belong to this
computer group.