Understanding the HCL DX 9.5 container deployment on Amazon EKS
This section describes the output and artifacts created when deploying HCL Digital Experience 9.5 container release in on Amazon Elastic Kubernetes Service (EKS).
./scripts/deployDx.sh dx14 1 AWS_OWNER_ID.dkr.ecr.us-east-2.amazonaws.com dxen v95_CF184_20200916-2009 dxh1-dam dx deploy-stg derby ambassador 154Namespace: dx14
- REPLICAS: 1
- Repository: AWS_OWNER_ID.dkr.ecr.us-east-2.amazonaws.com
- Image Name: dxen
- Image Tag: v95_CF184_20200916-2009
- Volume Name: dxh1-dam
- Storage Class Name: dx-deploy-stg
- Database Type: derby
-
namespace/awseks-demo created
serviceaccount/hcldx-cloud-operator created
role.rbac.authorization.k8s.io/hcldx-cloud-operator created
rolebinding.rbac.authorization.k8s.io/hcldx-cloud-operator created
deployment.apps/hcldx-cloud-operator created
dxdeployment.git.cwp.pnp-hcl.com/dx-deployment createdThe following artifacts are created during deployment:
Artifacts
Project/Namespace
The Project/Namespace gets created if it does not already exist.
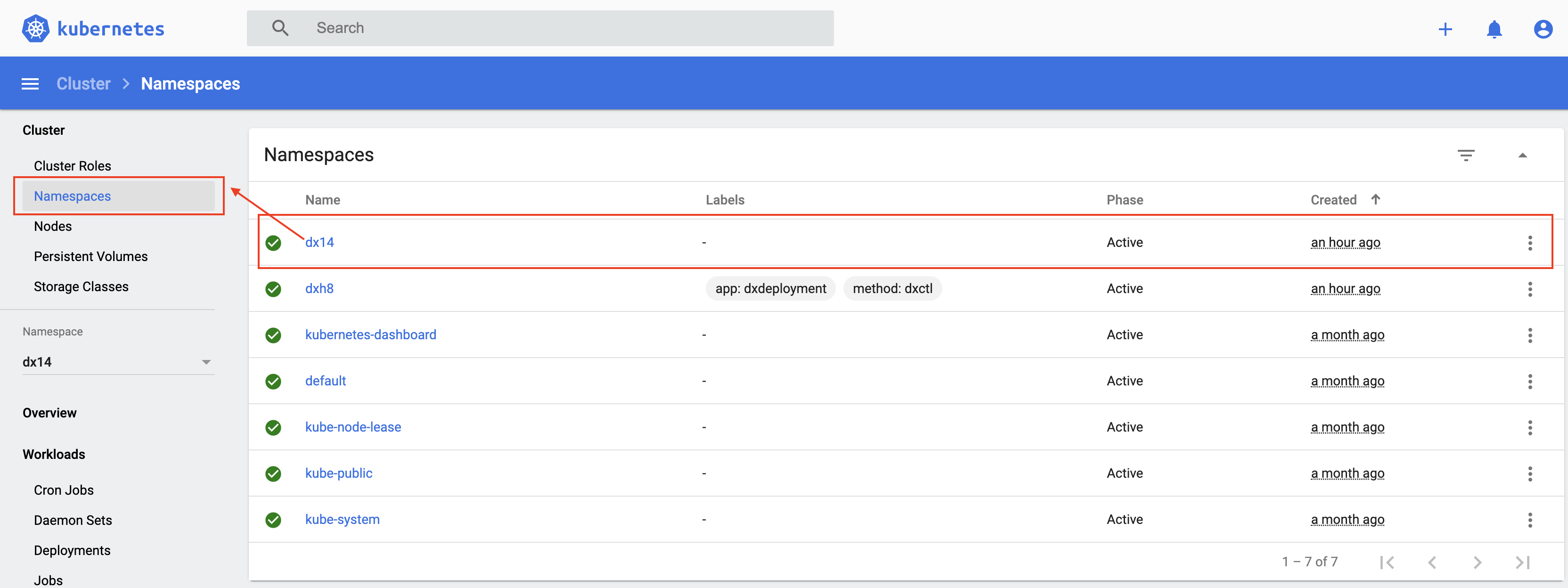
kubectl get namespaces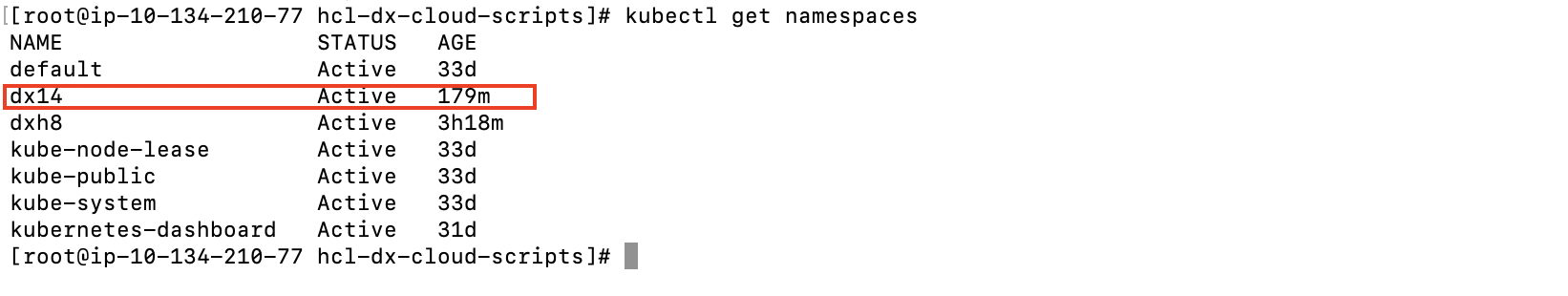
Service Account
Service Accounts for the operator and ambassador deployments.
kubectl get serviceaccounts -n dx14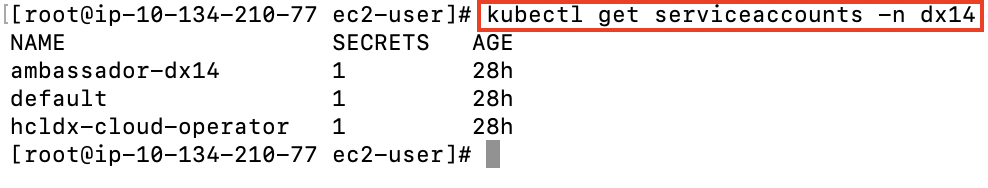
Role
kubectl get role -n dx14describe command.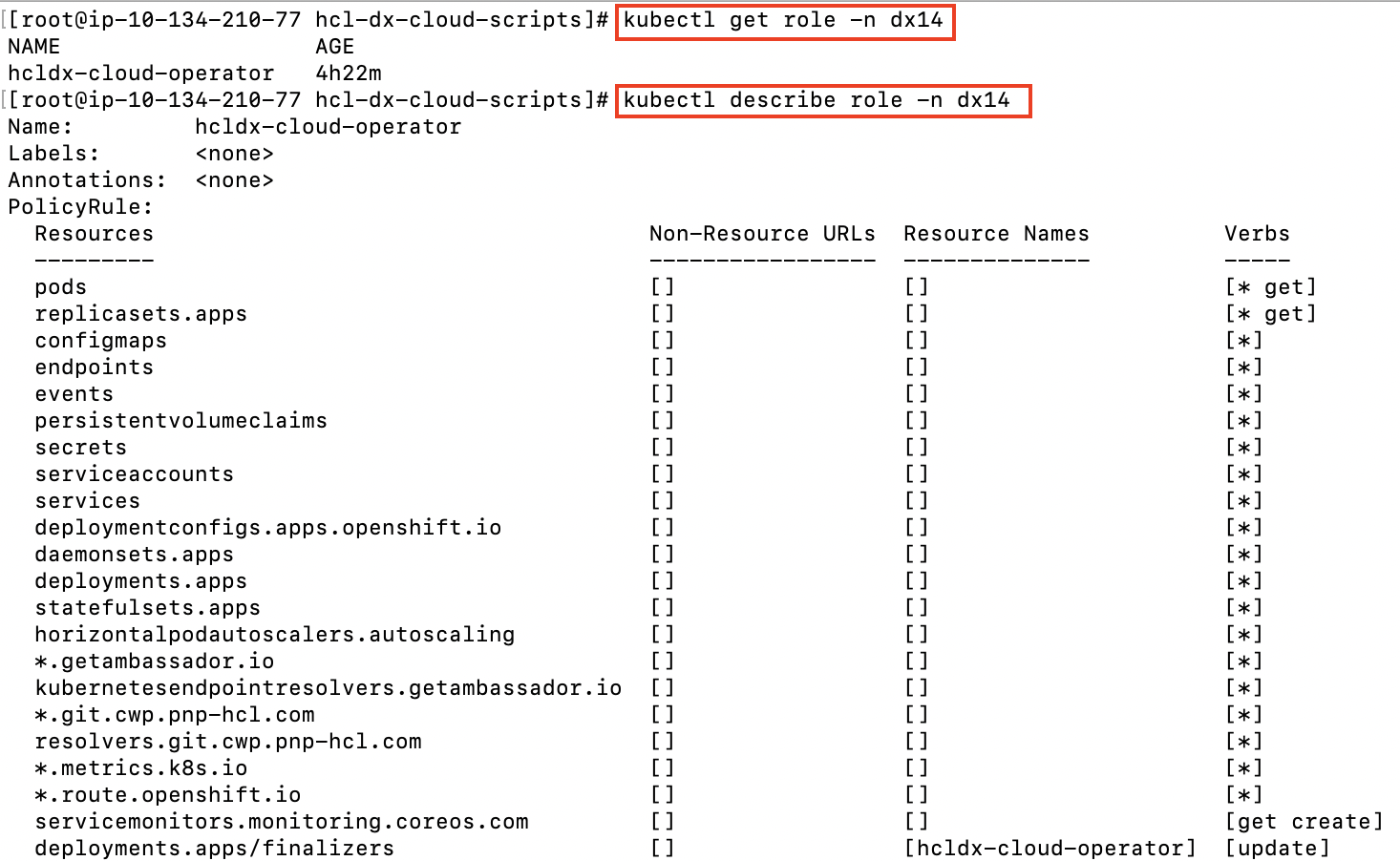
Role Binding
kubectl describe rolebinding -n dx14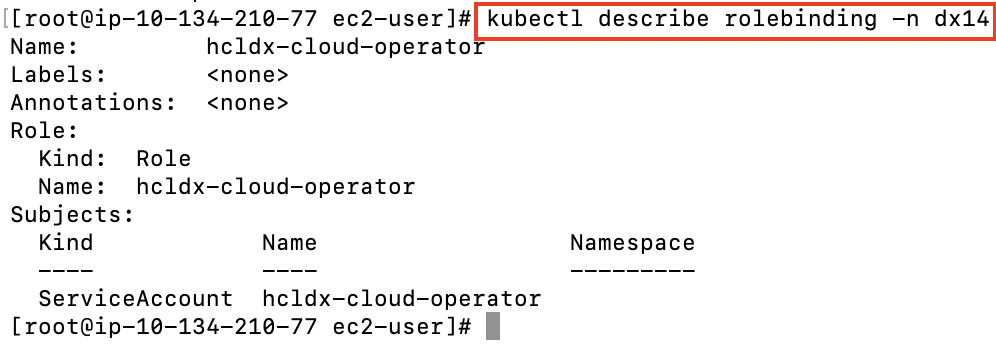
Deployment
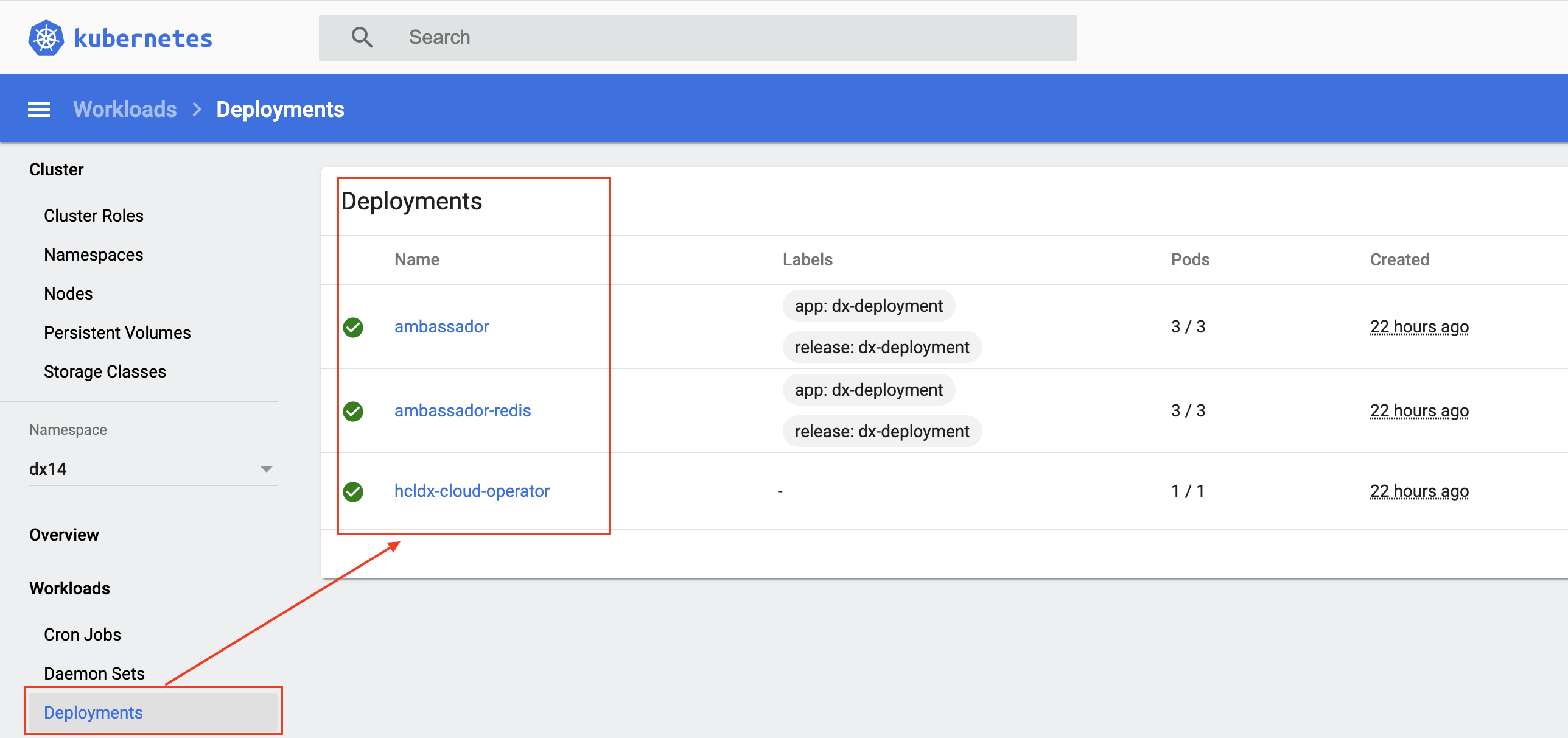
kubectl get deployment -n dx14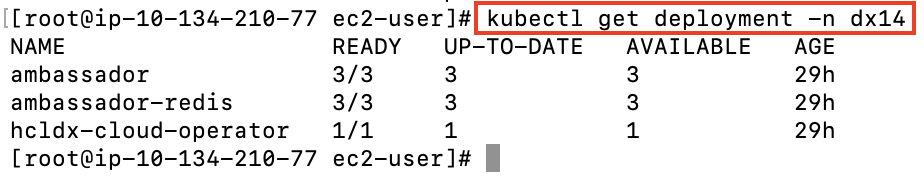
Replica Sets
Replica Sets based on the deployments of the ambassador and the operator, that maintains a stable set of replica pods.
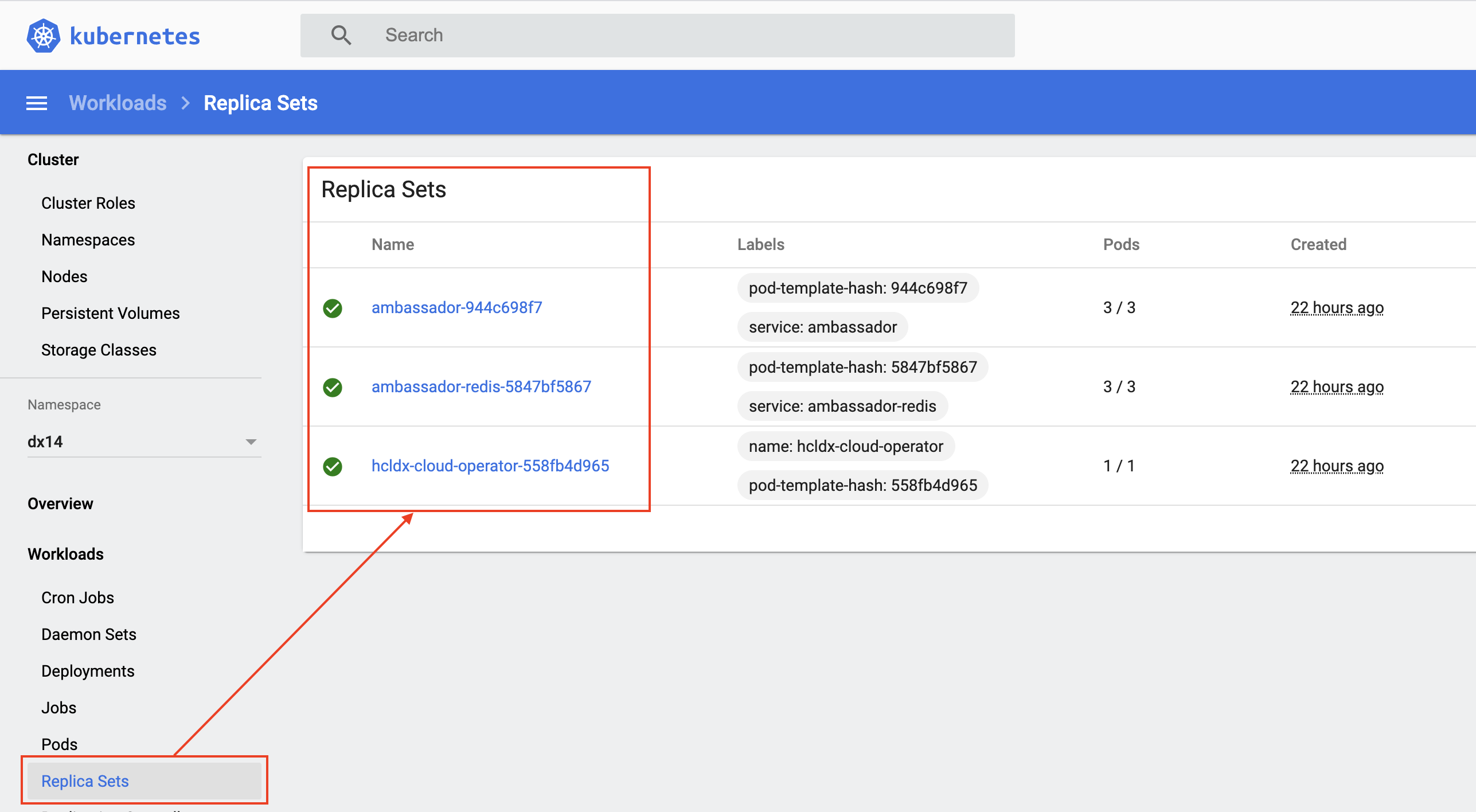
kubectl get replicaset -n dx14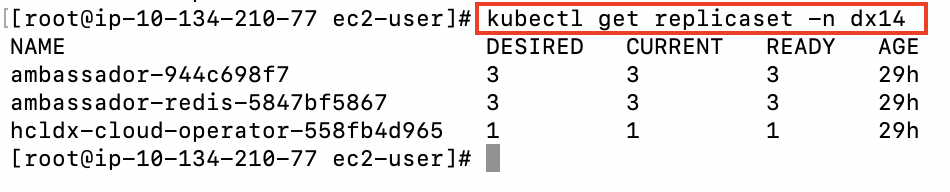
Metrics and Services
Services expose HCL Digital Experience running as part of the Stateful Set and provide metrics for the operator created.
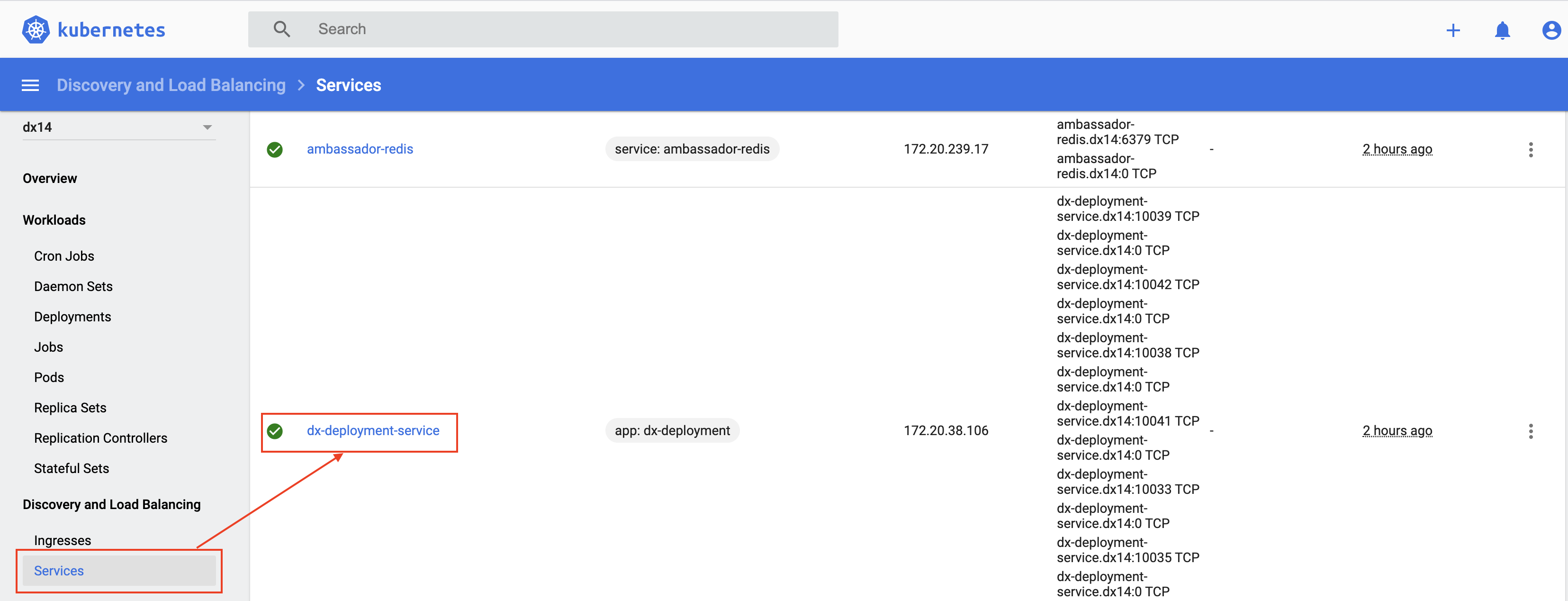
kubectl get service -n dx14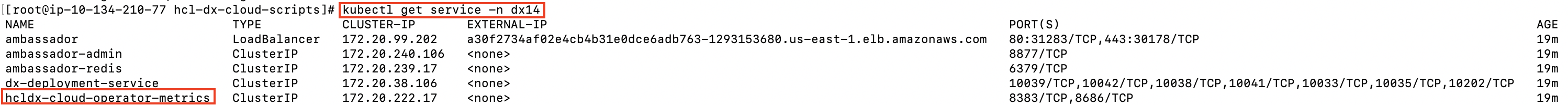
Secrets
There are several secrets that are created.
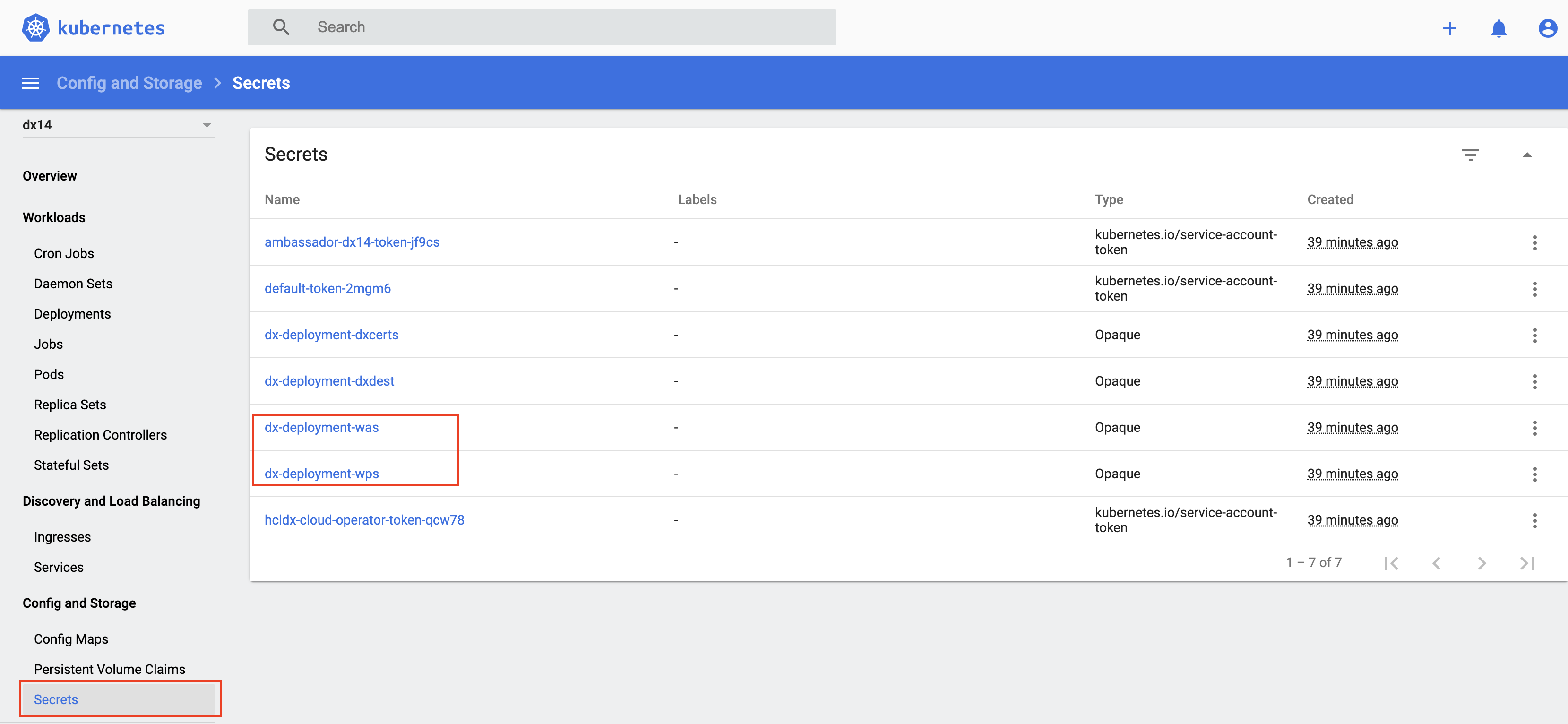
kubectl get secrets -n dx14kubectl describe secret dx-deployment-wps -n dx14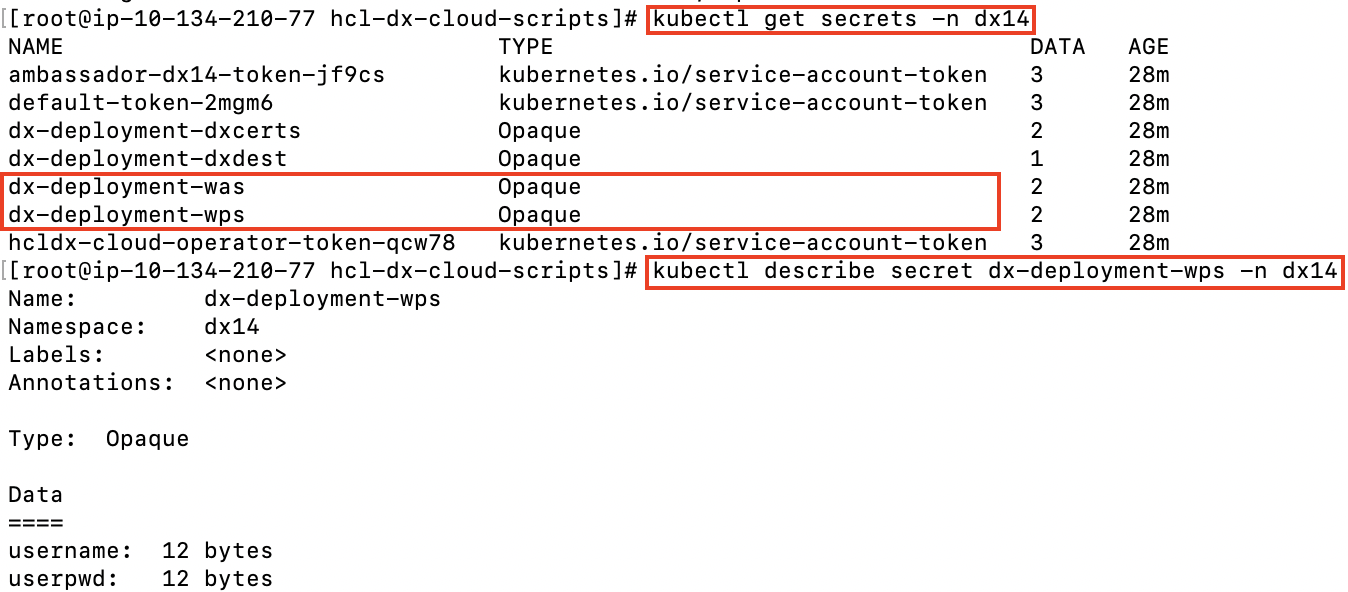
kubectl edit secret dx-deployment-wps -n dx14base64 encoded values when updating secrets. Most Linux operating
systems will allow you to generate base64 values with this
command:echo 'wpsadmin' | base64Config Map
A Config Map is created to handle clustering in scenarios where multiple operators are deployed.
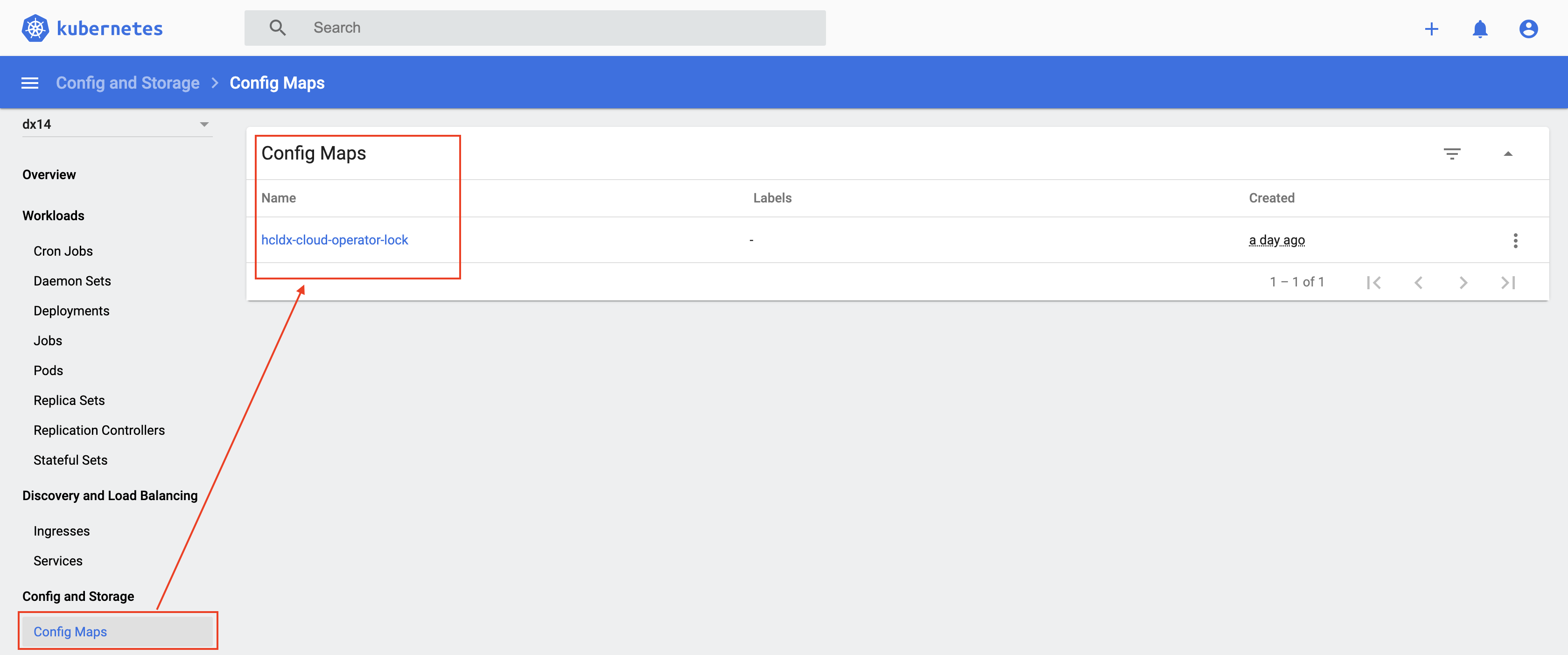
kubectl get configmap -n dx14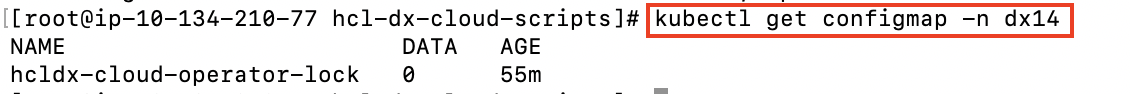
Persistent Volume Claims

kubectl get pvc -n dx14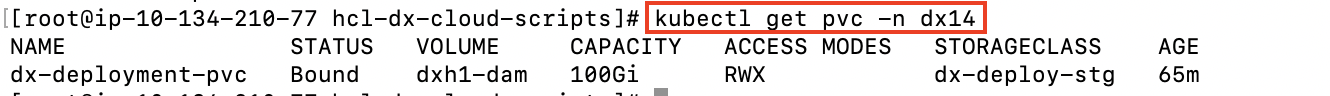
Stateful Set
A Stateful Set is created for the HCL Digital Experience core. A Stateful Set manages pods that are based on an identical container specification.
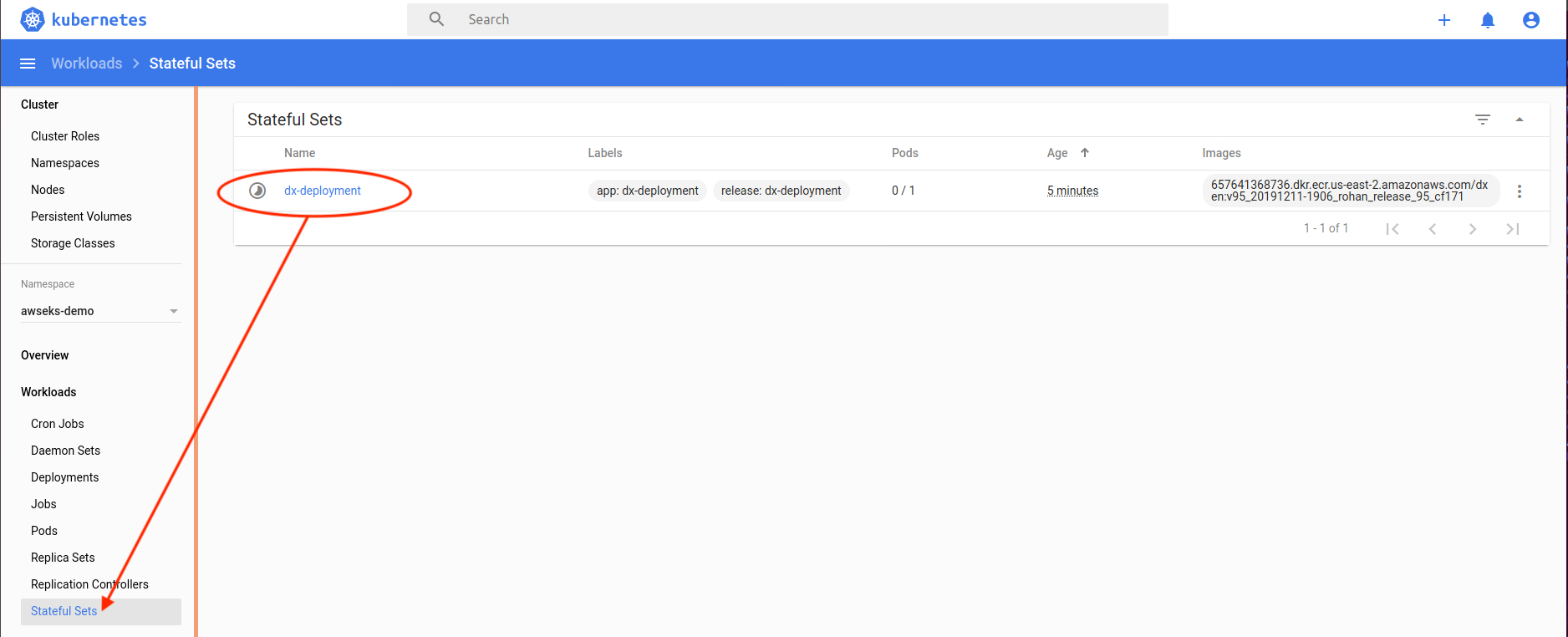
kubectl get statefulset -n dx14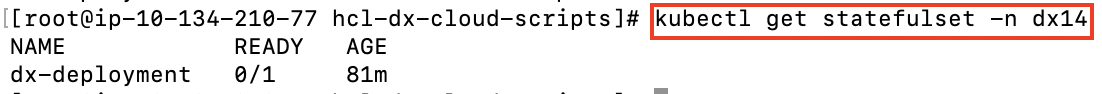
Pods
Pods are part of the Stateful Set, running HCL Portal.
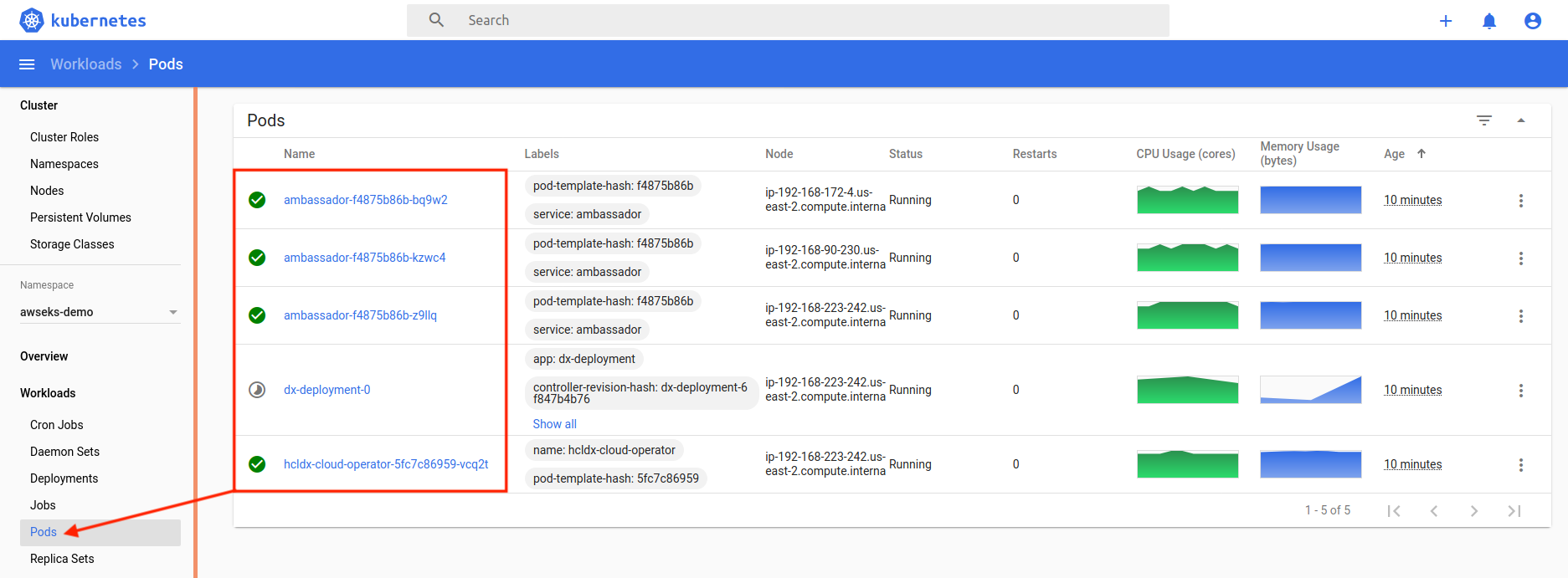
kubectl get pods -l app=dx-deployment -n dx14' (limits to pods in the
StatefulSetSpec)kubectl get pods -n dx14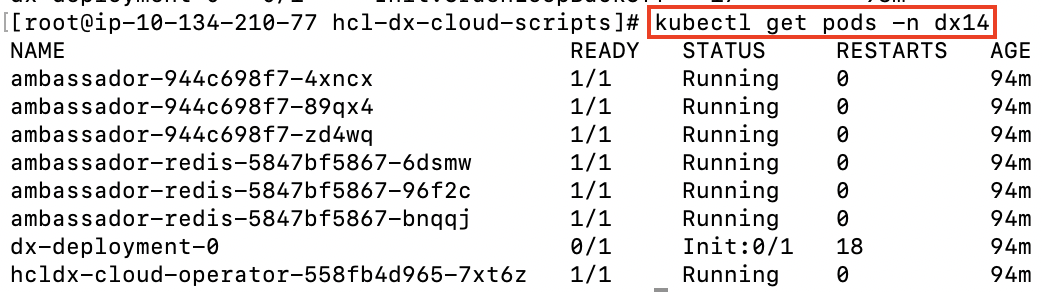
Ambassador
- Custom resources that help define Ambassador:
AuthService,ConsulResolver,KubernetesEndpointResolver,KubernetesServiceResolver,Mapping,Module,RateLimitService,TCPMapping,TLSContext,TracingService. - Ambassador deployment
- Ambassador replica set
- Ambassador pods (by default, 3)
- Ambassador service and Ambassador admin service
- An instance of TLS context
Figure 22. Sample with Kubernetes Dashboard 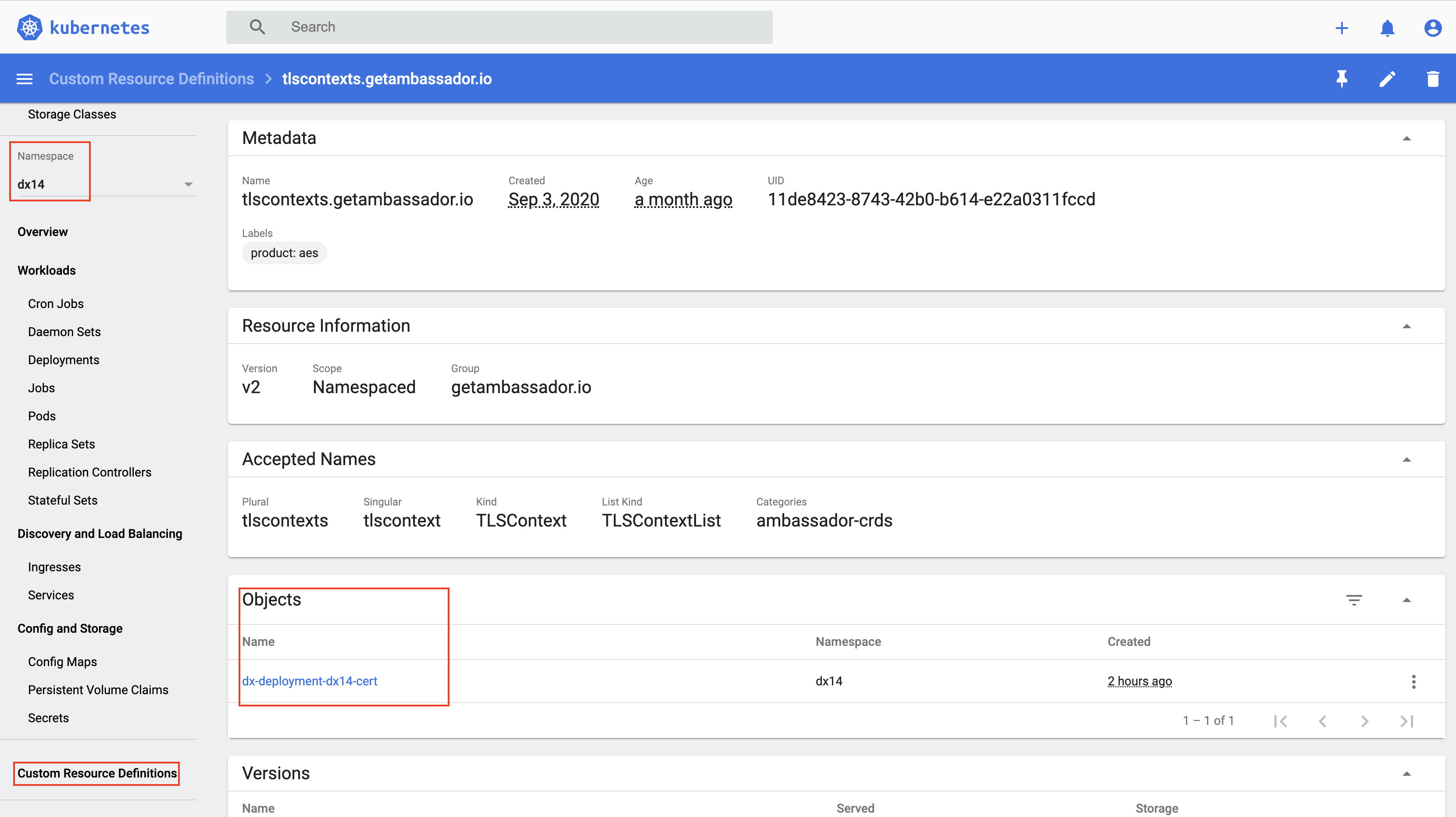
kubectl describe TLSContext -n dx14Figure 23. TLS Context sample with CLI 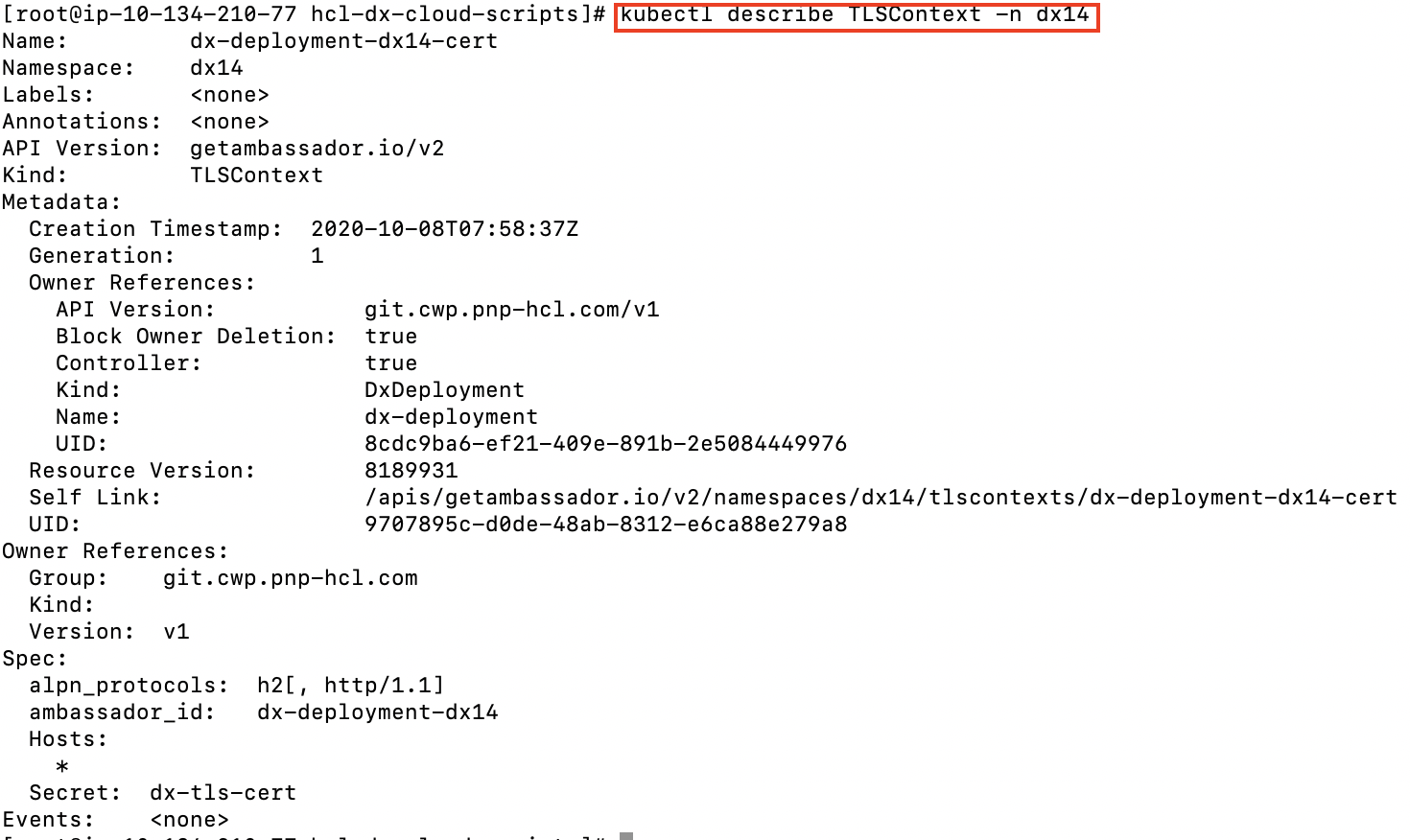
Mapping
An instance of Mapping for each target: DX Home Secure, WAS Home Secure, etc.
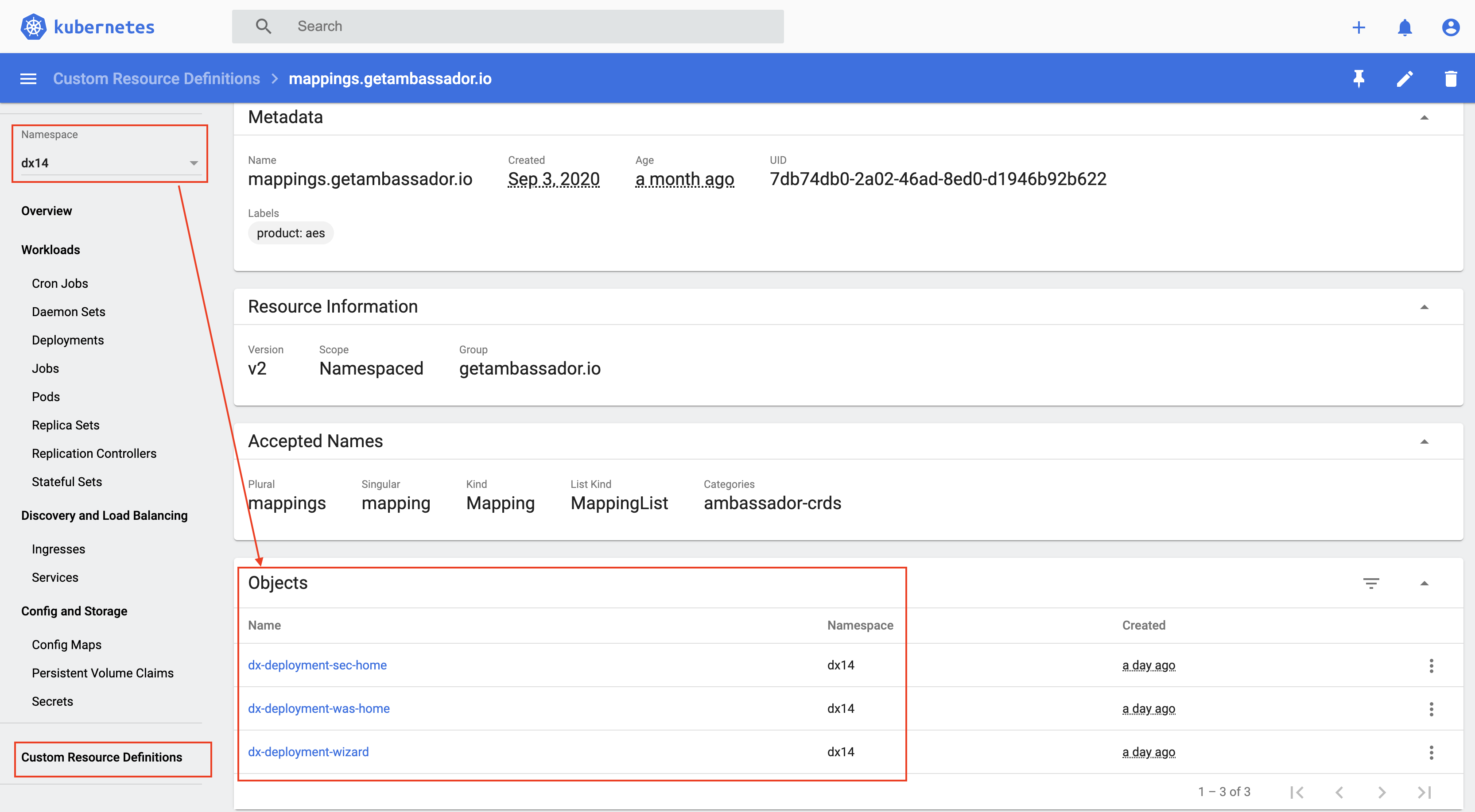
kubectl get mapping -n dx14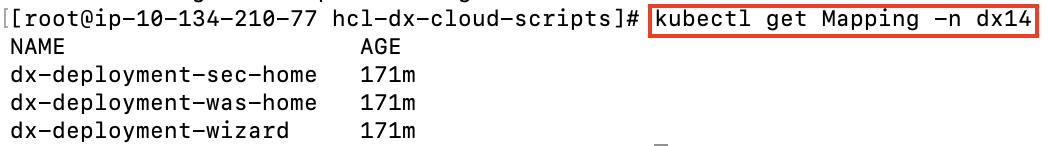
Extras
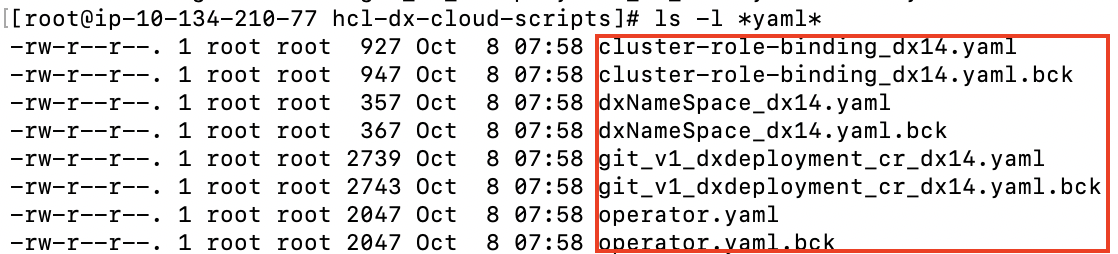
- File 1
dxNameSpace_NAMESPACE.yamlcan be used to delete thenamespace/projectif needed. - File 2
git_v1_dxdeployment_cr_NAMESPACE.yamlis a representation of the last deployed deployment for the givennamespace/project.