Troubleshooting LDAPS connection
Condition
LDAP connection failure.
Cause
It is optional to configure MDM server with LDAP credentials. If you enter wrong values or values in incorrect format, it displays an error as “invalid”. However, the Fixlet actions complete successfully, which might cause connection issues at times.
Solution
Using the command-line utility BESmdmldaputil, you can validate LDAP
parameters, email, and user authentication to troubleshoot your LDAP connection
issues.
Note: If you change LDAP parameters in .env file, you must
restart
To validate LDAP parameters, run the following command from the MDM
server:idservice for the changes to take
effect.docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil <options>-a : Authenticate user
-c : Clear cache
-e : Validate email
-f : Get all AD/AAD groups
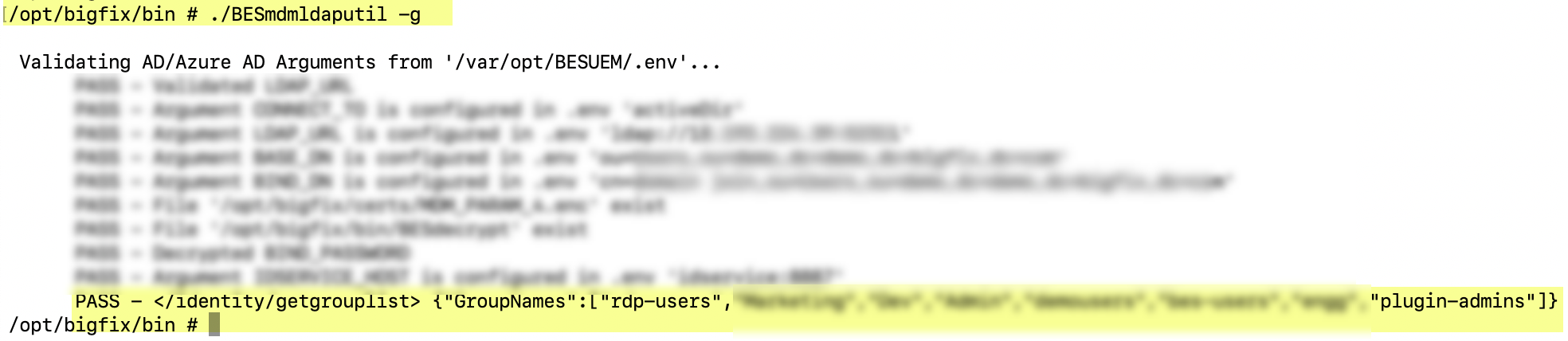
-g : Get group list
-h : Help Content
-l : List cache names
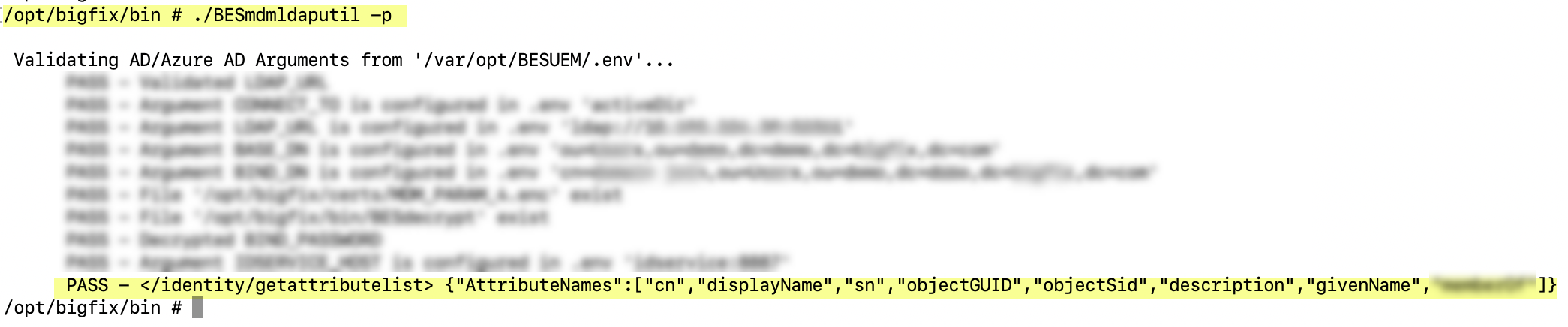
-p : Get attribute list
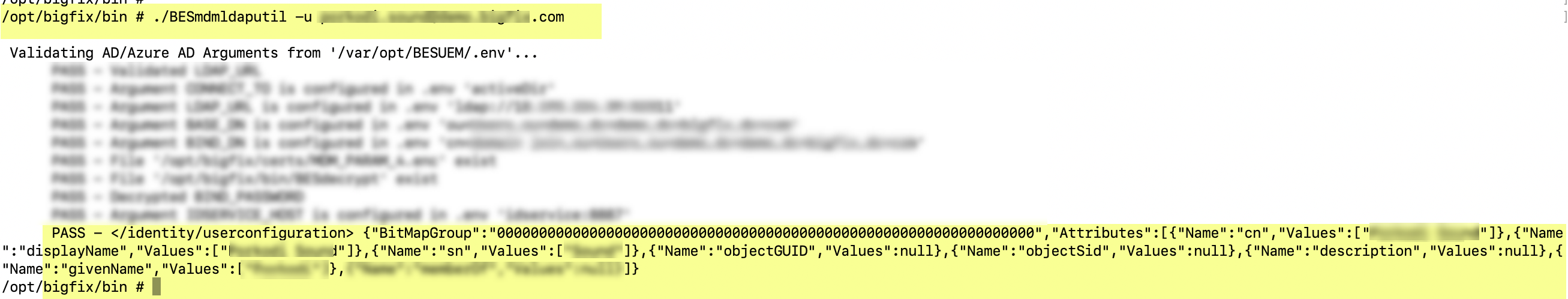
-u : Get user configuration
-v : Validate .env variables, values, and AD/Azure AD connectivity
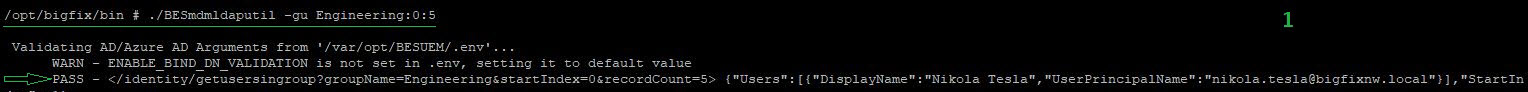
-gu : get all users in a group
-sg : Set groups in AD/AAD
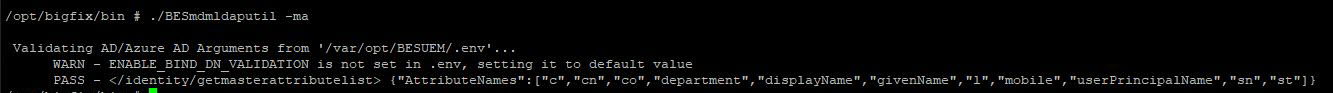
-ma : Get master attribute list
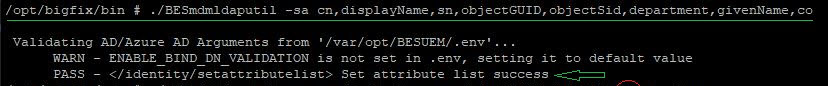
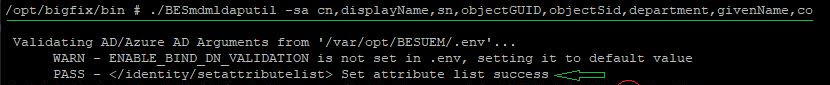
-sa : Set attributes
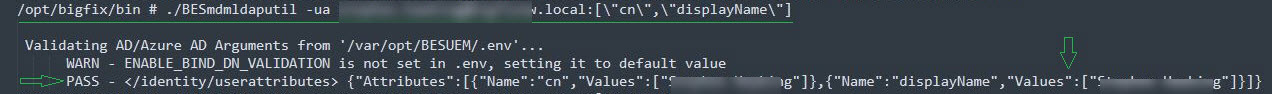
-ua : Set user attributes in AD/AAD
-ubg : Get user bitmap group
-ug : List all group names of the userThe following are some of the examples on how to use the
options;
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -h
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -v
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -e user@example.com
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -a username:password
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -e user@example.com -a username:password
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -c groupNames
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -l
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -f 1:10
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -p
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -u user@example.com
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -gu groupname:1:100
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -sg groupname1,groupname2,groupname3
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -ma
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -sa attributeName1,attributeName2,attributeName3
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -ua testuser@test.com:[\"displayName\",\"cn\"]
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -ubg exampleuser@bigfix.local
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -ug username(or)UPN:1:100- Pagination
- You can define the number of records that can be displayed as an output by specifying
the starting record number and the ending record number in the format <start
record:end record>. The starting number of the record is 0. Pagination is supported for
the options -f, -gu, and -ug. For example if you want to display 500 group names from
the 11th bit onwards, run the following
command.
docker exec -it idservice /opt/bigfix/bin/BESmdmldaputil -gu groupname:10:510
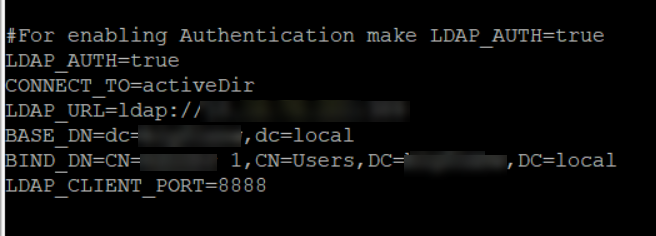
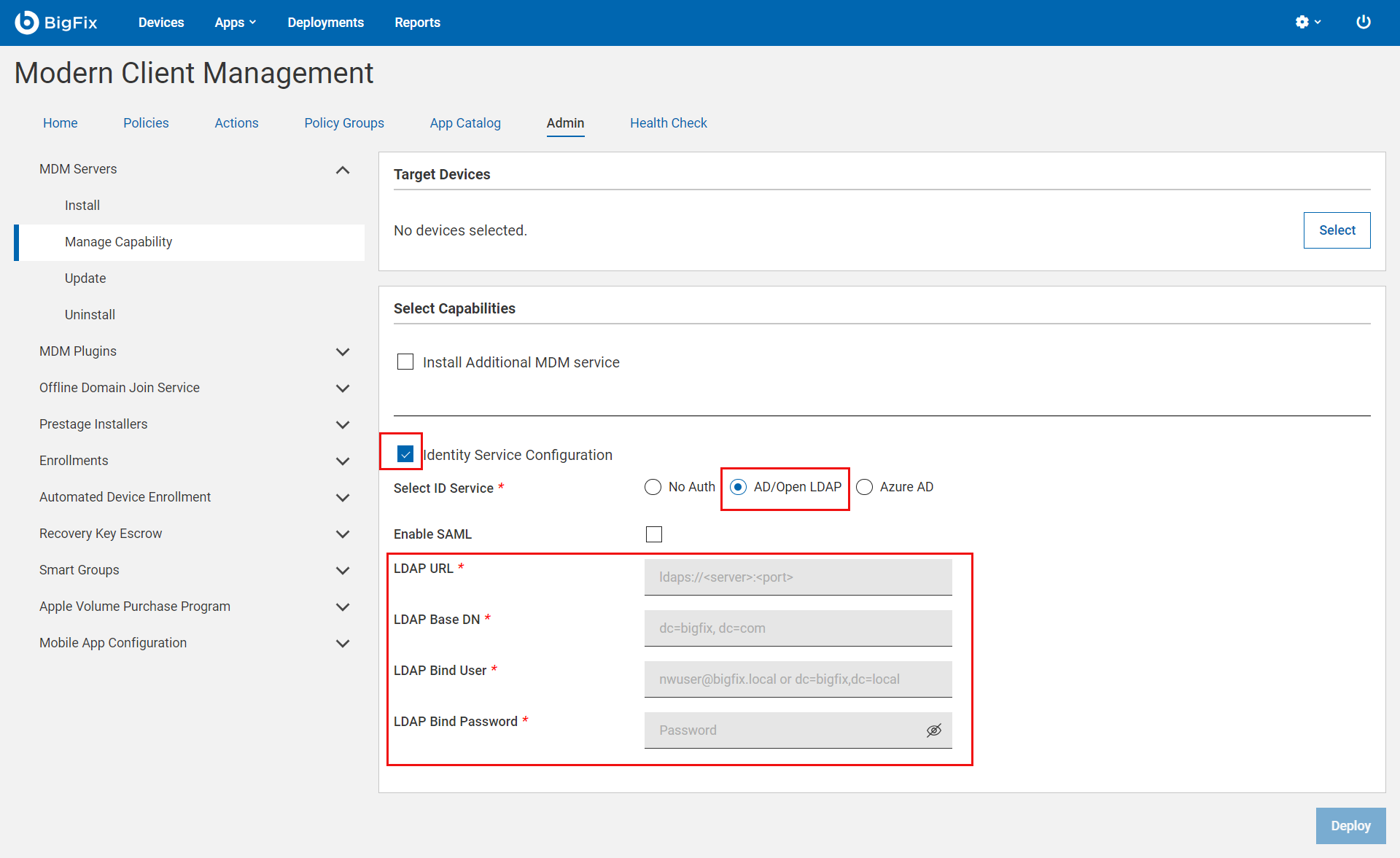
- This utility validates LDAP parameters that were provided through WebUI Identity Service Configuration.
as shown in the following image:
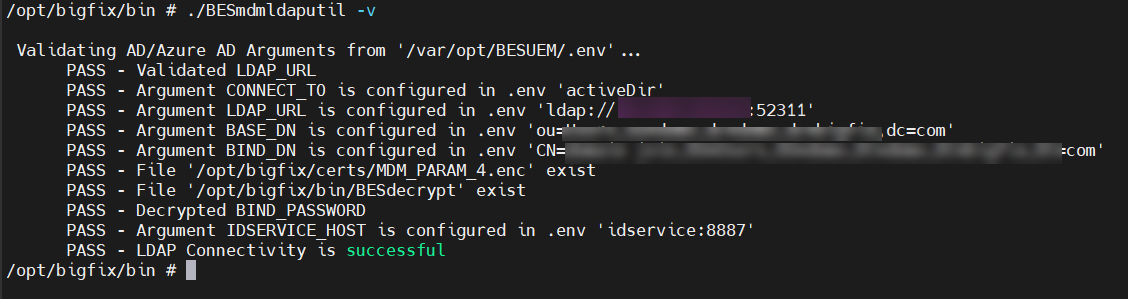
- The following is an example of the validation messages when you use the option -v to
validate LDAP env arguments.
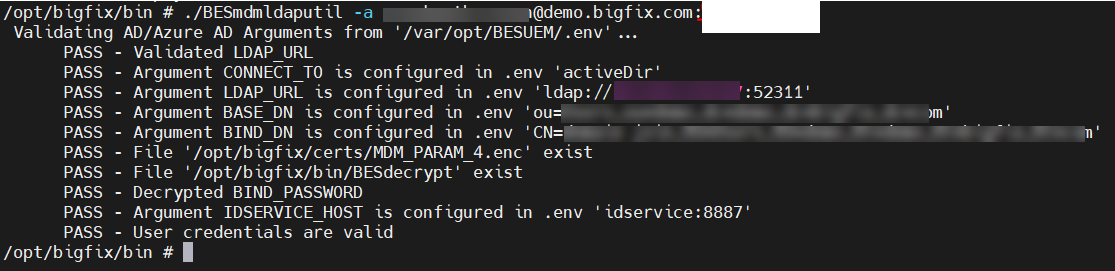
- The following is an example of the validation messages when you use the option -a to
authenticate a specific user.
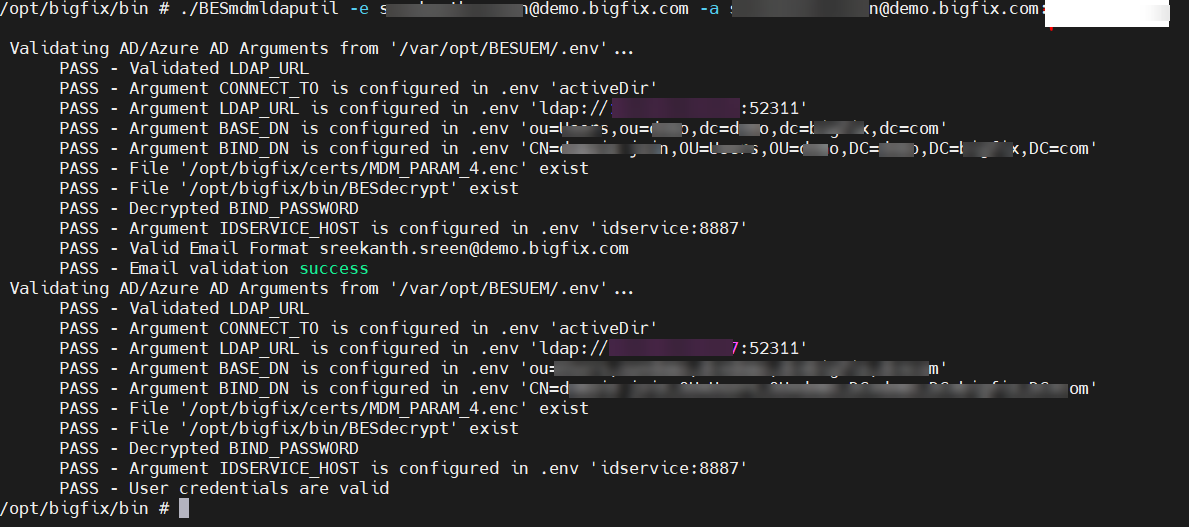
- You can also combine more than one option to get the desired result. The following
image shows the result for the options -e and -a for the values provided:
- The following is an example to clear cache with the option -c.
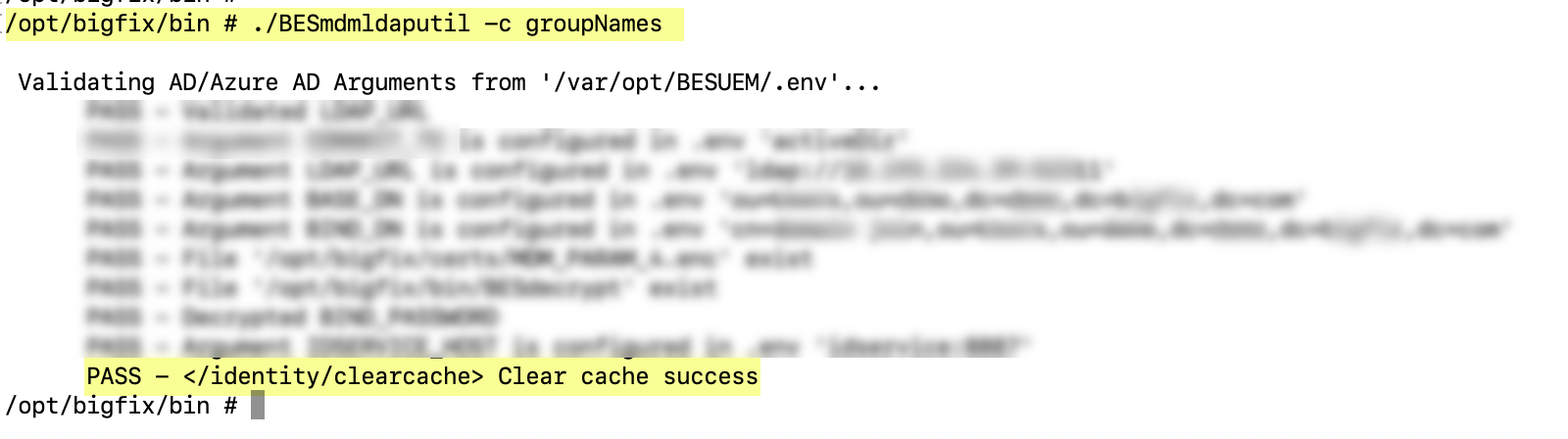
- The following is an example to list cache names with the option -l.

- The following is an example to list all group names with the option -f.
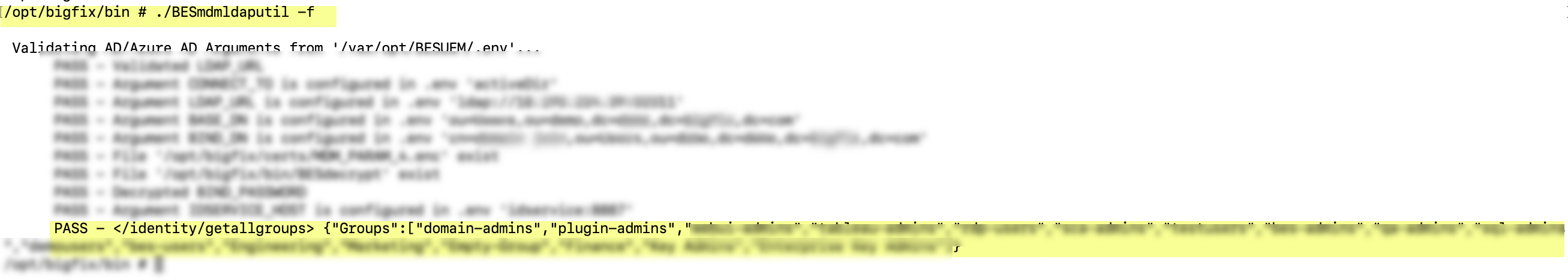
- The following is an example to list attributes names with the option -p.
- The following is an example to get user configuration with the option -u.
- The following is an example to get group names with the option -g.
- The following is an example to get all users in a group with the option -gu.
- The following is an example to set groups in AD/AAD with the option -sg.
- The following is an example to get master attribute list with the option -ma.
- The following is an example to set attributes in AD/AAD with the option -sa.
- The following is an example to set user attributes in AD/AAD with the option
-ua.
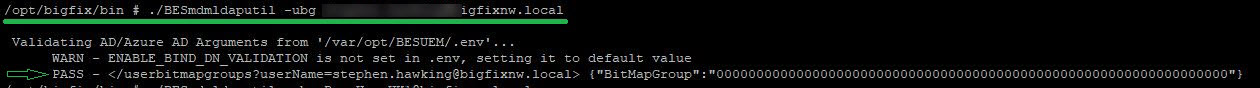
- The following is an example to get user bitmap group with the option -ubg.
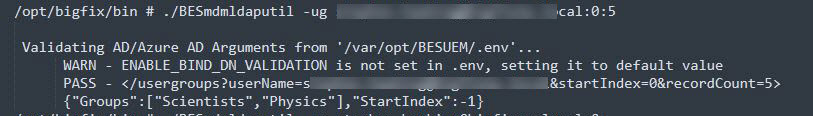
- The following is an example to list all group names of the user with the option
-ug.